
Google has discovered the first zero-day exploit developed by AI and has successfully prevented a planned large-scale exploitation event.
**Summary**: Google has identified a zero-day exploit believed to be developed using artificial intelligence and successfully disrupted a planned mass exploitation event. The GTIG report highlights the involvement of state-sponsored actors from China, North Korea, and Russia utilizing AI for vulnerability research, autonomous malware creation with Google's Gemini API, and attacks on the AI software supply chain.
Google has detected what it considers the first zero-day exploit crafted with AI. The malicious actor behind this exploit intended to use it for a large-scale exploitation event. The vulnerability was uncovered by Google’s Threat Intelligence Group before it was activated, allowing them to collaborate with the affected vendor to correct it and prevent its use. This exploit, which is a Python script designed to circumvent two-factor authentication on a widely used open-source system administration tool, exhibited fabricated CVSS scores, educational comments, and the systematic formatting typical of output from large language models. Google is confident that an AI model was used to identify and weaponize this flaw.
This information is derived from a report issued by Google’s Threat Intelligence Group on Monday, detailing the transition from experimental AI-enhanced hacking to what GTIG refers to as the “industrial-scale application of generative models in adversarial contexts.” State-sponsored groups from China and North Korea are employing AI for vulnerability assessments, while Russian-linked threat actors are using AI-generated decoy code in attacks against Ukrainian targets. An Android malware named PROMPTSPY utilizes Google’s Gemini API to autonomously navigate victim’s devices, collect biometric information, and prevent its own removal. The cybersecurity race involving AI that experts warned about is now a reality, as indicated in Google’s incident response records.
**The Zero-Day**:
The exploit in question addressed a semantic logic flaw rather than a memory corruption issue or input sanitization error; it was a high-level design flaw due to a hardcoded trust assumption within the two-factor authentication logic. Conventional vulnerability scanners and fuzzers, optimized for detecting crashes and data flow issues, overlook this type of flaw—which is detectable by large language models. These models can perform contextual reasoning, understanding the developer’s intent and correlating the authentication logic with contradicting hardcoded exceptions. Thus, the model uncovered a hidden logic error that appeared functionally correct to conventional scanners but was fundamentally flawed from a security standpoint.
GTIG coordinated responsibly with the vendor affected to disclose the flaw, though they do not believe the Gemini model was utilized in the exploit. Google notes that the group responsible for this exploit has a history of significant incidents and broad exploitation attempts. Proactive measures thwarted the planned mass exploitation. This indicates that AI has reached a new capability level; it can identify vulnerabilities that evade human detection and traditional tools and is being used by criminal entities for large-scale exploits.
**The Autonomous Malware**:
PROMPTSPY is an Android backdoor first reported by ESET in February 2026. Initial reports highlighted its use of the Gemini API to ensure persistence by pinning the malicious app in the recent applications list. However, Google’s analysis has unveiled much more advanced capabilities.
The malware features an autonomous module named GeminiAutomationAgent, which serializes the device’s user interface hierarchy into an XML-like format through the Accessibility API and forwards it to the gemini-2.5-flash-lite model. The model provides structured JSON responses containing action types and spatial coordinates, which PROMPTSPY interprets to emulate physical maneuvers like clicks, swipes, and navigation. The AI assesses the device’s condition and generates commands in real time, operating without human input.
PROMPTSPY can gather victim biometric data to replicate authentication actions and regain access to compromised devices. If a victim attempts to uninstall it, the malware can identify the uninstall button's coordinates on the screen and create an invisible overlay that intercepts touch entries, rendering the button seemingly unresponsive. Its command and control infrastructure can also be flexibly updated in real-time, meaning that blocking specific endpoints is not enough to neutralize the backdoor. Google has now disabled the related assets and confirmed that no apps containing PROMPTSPY are available on Google Play.
**The State Actors**:
State-sponsored threat actors from China and North Korea are increasingly using AI for sophisticated vulnerability research. GTIG noted that the Chinese-linked group UNC2814 has directed Gemini to function as a “senior security auditor” and “C/C++ binary security expert” to assist in vulnerability assessments of TP-Link firmware and file transfer protocols. North Korea’s APT45 has executed thousands of repetitive prompts to recursively analyze various CVEs and affirm proof-of-concept exploits, constructing an extensive arsenal of exploit capabilities that would be challenging to manage without AI support.
Chinese threat actors have experimented with a specific vulnerability repository called wooyun-legacy, a Claude code skill plugin that offers a distilled knowledge base of over 85,000 real-world vulnerability cases accumulated by the Chinese bug bounty platform WooYun from 2010 to 2016. By conditioning an AI model with this
Other articles
 The upcoming Chrome update from Google is significant for Android users.
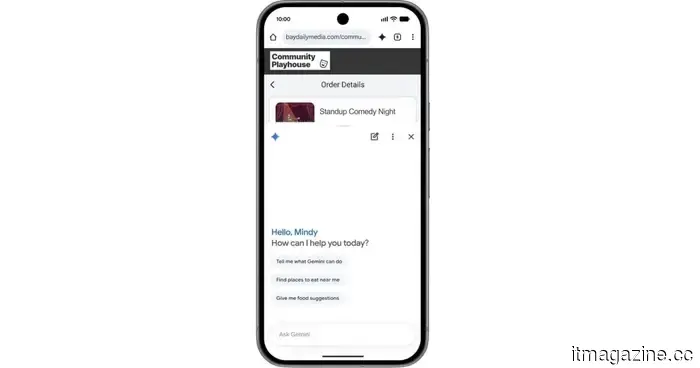
Chrome on Android is receiving a significant AI enhancement with Gemini at its center, transforming the browser into a more useful assistant capable of comprehending pages, managing tasks, and streamlining your web experience.
The upcoming Chrome update from Google is significant for Android users.
Chrome on Android is receiving a significant AI enhancement with Gemini at its center, transforming the browser into a more useful assistant capable of comprehending pages, managing tasks, and streamlining your web experience.
 Kevin Hartz's A* adopts a 'less-is-more' strategy with its new $450 million fund.
Kevin Hartz's A* has finalized a $450 million fund, presented as a response to AI megafunds pursuing billion-dollar valuations at all stages.
Kevin Hartz's A* adopts a 'less-is-more' strategy with its new $450 million fund.
Kevin Hartz's A* has finalized a $450 million fund, presented as a response to AI megafunds pursuing billion-dollar valuations at all stages.
 Nadella was concerned that Microsoft might end up being 'the next IBM' following the unveiling of a $92 billion return projection for OpenAI during the trial.
Microsoft CEO Satya Nadella stated during the Musk v. Altman trial that he was concerned his company might follow in IBM's footsteps. A memo from Brad Smith estimated that OpenAI's $13 billion investment could yield a $92 billion return.
Nadella was concerned that Microsoft might end up being 'the next IBM' following the unveiling of a $92 billion return projection for OpenAI during the trial.
Microsoft CEO Satya Nadella stated during the Musk v. Altman trial that he was concerned his company might follow in IBM's footsteps. A memo from Brad Smith estimated that OpenAI's $13 billion investment could yield a $92 billion return.
 eBay turns down GameStop's $56 billion offer as
The board of eBay has dismissed GameStop's $56 billion acquisition proposal, describing it as neither credible nor appealing, due to concerns over financing uncertainty and leverage.
eBay turns down GameStop's $56 billion offer as
The board of eBay has dismissed GameStop's $56 billion acquisition proposal, describing it as neither credible nor appealing, due to concerns over financing uncertainty and leverage.
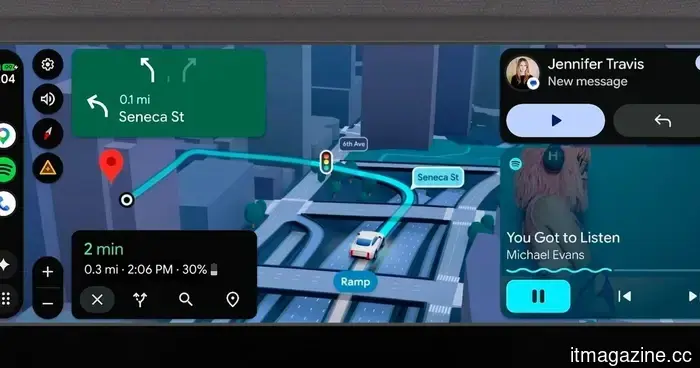 This update to Android Auto aims to alter the way you operate your vehicle and interact with it.
Android Auto is undergoing a significant enhancement that extends beyond mere design changes, offering improved navigation, enhanced entertainment options, and a more supportive driving experience.
This update to Android Auto aims to alter the way you operate your vehicle and interact with it.
Android Auto is undergoing a significant enhancement that extends beyond mere design changes, offering improved navigation, enhanced entertainment options, and a more supportive driving experience.
 Signal Messenger aims to safeguard you against phishing through these new changes within the app.
Signal has introduced new safety features within the app to assist users in identifying and steering clear of phishing and social engineering attacks, including individuals pretending to be Signal.
Signal Messenger aims to safeguard you against phishing through these new changes within the app.
Signal has introduced new safety features within the app to assist users in identifying and steering clear of phishing and social engineering attacks, including individuals pretending to be Signal.
Google has discovered the first zero-day exploit developed by AI and has successfully prevented a planned large-scale exploitation event.
Google's GTIG discovered the first zero-day exploit created with AI and prevented a widespread exploitation incident. The report indicates that state actors are leveraging AI for vulnerability research and autonomous malware development.
