More than 30 WordPress plugins purchased on Flippa have been compromised through a backdoor in a supply chain attack.
An attacker acquired over 30 WordPress plugins from the Essential Plugin portfolio on Flippa for a six-figure sum, inserted a PHP deserialization backdoor in August 2025, and then activated it eight months later to deliver cloaked SEO spam specifically to Googlebot. On 7 April 2026, WordPress.org removed 31 plugins from the platform. In the same week, Smart Slider 3 Pro, which has more than 800,000 installations, was compromised through its update infrastructure. These incidents highlight a significant vulnerability: WordPress lacks a process to review transfers of plugin ownership or to mandate code signing for updates.
The buyer, known only as “Kris” and associated with a background in SEO, cryptocurrency, and online gambling marketing, purchased the entire Essential Plugin portfolio on Flippa in early 2025. Flippa was so pleased with the sale that it published a case study about the transaction in July 2025, by which time the backdoor had already been established.
The malicious code made its way into version 2.6.7 of the plugins, released on 8 August 2025, which included a changelog statement that read “Check compatibility with WordPress version 6.8.2.” Hidden within that innocuous note were 191 additional lines of PHP, including a deserialization backdoor allowing remote code execution. The exploit remained inactive for eight months, gradually gaining trust due to the absence of any observable issues, before it was activated on 5 and 6 April 2026.
On 6 April, the injection lasted for six hours and 44 minutes, between 04:22 and 11:06 UTC. During this timeframe, a command-and-control domain, analytics.essentialplugin.com, began distributing payloads to every site using one of the compromised plugins. The plugins’ internal wpos-analytics module downloaded a file named wp-comments-posts.php and utilized it to inject PHP code directly into wp-config.php, a critical file in any WordPress installation.
The nature of the payload was marked by its sophistication and restraint. It retrieved spam links, redirects, and fake pages from the command-and-control server, serving them exclusively to Googlebot. Site owners browsing their own websites noticed nothing amiss. The harmful content was only encountered by search engine crawlers, employing cloaking techniques intended to influence search rankings while avoiding human detection for as long as possible.
The command-and-control (C2) infrastructure was designed to evade disruption. Instead of using a conventional domain that could be seized or blacklisted, the payload resolved its command server through an Ethereum smart contract, querying public blockchain RPC endpoints. Conventional domain seizures, typically used to disrupt botnets and spam operations, would not suffice in this case.
This attack seized upon what essentially represents a policy void within the WordPress ecosystem. While WordPress.org vets new plugin submissions before they are included in the directory, no extra review occurs when an existing plugin is sold. There is no notification regarding a “change of control” sent to the vast number of sites utilizing the affected plugins. The new owner inherits the previous developer’s commit access, reputation, and the implicit trust of every site administrator who enabled automatic updates.
This is not merely a theoretical issue but a structural flaw. WordPress underpins approximately 43 percent of all websites online. Its plugin ecosystem comprises more than 60,000 plugins, many maintained by individual developers or small teams who may sell their projects if they lose interest, need financial support, or simply move on. Each of these transactions presents an opportunity for similar attacks: acquire trust, bide time, and then exploit.
WordPress.org responded promptly to the Essential Plugin breach once detected. On 7 April, the plugins team permanently removed 31 plugins associated with the affected author. A subsequent update, version 2.6.9.1, disabled the phone-home mechanism. However, it did not address the injected code in wp-config.php, which meant that sites already compromised continued to serve hidden spam to search engines even after the update. Comprehensive remediation requires a manual inspection of wp-config.php, a step many site operators running small businesses on WordPress may not know how to execute.
The Essential Plugin incident coincided with a separate supply chain attack on Smart Slider 3 Pro, a popular WordPress slider plugin with over 800,000 active installations. In that case, attackers breached Nextend's update infrastructure and pushed a malicious version, 3.5.1.35, through official update channels. Any site that auto-updated in the roughly six-hour window before detection received a complete remote access toolkit capable of creating unauthorized administrator accounts, exfiltrating database credentials, and establishing persistent backdoors at multiple locations across the file system.
While the two attacks employed different methods—one taking advantage of an ownership transfer and the other a server compromise—they both uncovered the same fundamental weakness: the WordPress update process implicitly trusts the source of an
Other articles
 FCC approves Netgear while the ban on routers made overseas remains intact.
Netgear is the first retail router brand to receive an FCC exemption from the ban on foreign-made routers, allowing it a smoother path to continue introducing new models, while competitors encounter more stringent challenges.
FCC approves Netgear while the ban on routers made overseas remains intact.
Netgear is the first retail router brand to receive an FCC exemption from the ban on foreign-made routers, allowing it a smoother path to continue introducing new models, while competitors encounter more stringent challenges.
 Nissan has unveiled the Juke EV, and I sincerely hope this daring design remains.
Nissan has unveiled the third-generation Juke as an all-electric crossover for Europe, and its striking new design is undoubtedly the most captivating aspect of the vehicle.
Nissan has unveiled the Juke EV, and I sincerely hope this daring design remains.
Nissan has unveiled the third-generation Juke as an all-electric crossover for Europe, and its striking new design is undoubtedly the most captivating aspect of the vehicle.
 Wayve expands its $1.2 billion funding round with an additional $60 million from AMD, Arm, and Qualcomm.
Wayve has secured $60 million from AMD, Arm, and Qualcomm Ventures, thereby expanding its Series D funding round to $1.2 billion. Plans for robotaxi trials with Uber are set for Tokyo and London starting in 2026.
Wayve expands its $1.2 billion funding round with an additional $60 million from AMD, Arm, and Qualcomm.
Wayve has secured $60 million from AMD, Arm, and Qualcomm Ventures, thereby expanding its Series D funding round to $1.2 billion. Plans for robotaxi trials with Uber are set for Tokyo and London starting in 2026.
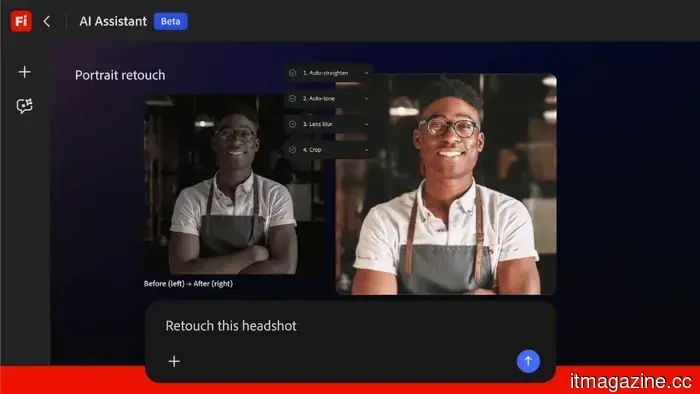 Adobe introduces the Firefly AI Assistant to manage tasks throughout Creative Cloud.
Adobe's Firefly AI Assistant employs natural language to coordinate activities across Photoshop, Premiere, Lightroom, and Illustrator. It will soon be available in public beta and includes integration with Anthropic Claude.
Adobe introduces the Firefly AI Assistant to manage tasks throughout Creative Cloud.
Adobe's Firefly AI Assistant employs natural language to coordinate activities across Photoshop, Premiere, Lightroom, and Illustrator. It will soon be available in public beta and includes integration with Anthropic Claude.
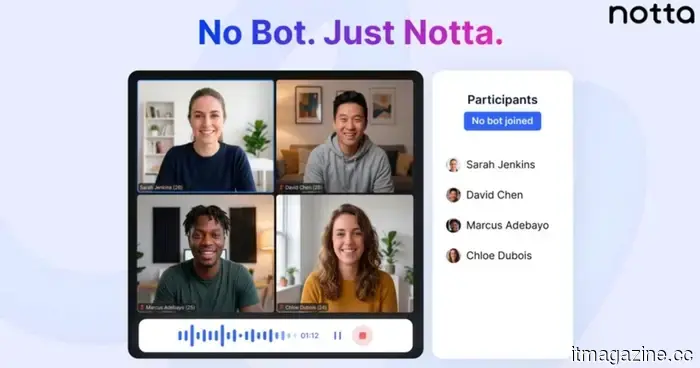 Notta Introduces Meeting Recording Without Bots for Mac and Windows
Notta’s latest Bot-Free mode is transforming the way professionals capture and transcribe meetings—eliminating interruptions, waiting times, and those uncomfortable moments of “who invited that person?” If you've ever utilized an AI meeting assistant, you're familiar with the scenario. You're engaged in a conversation, the dialogue is starting to pick up speed, and suddenly, a bot enters the call. Everything comes to a halt. […]
Notta Introduces Meeting Recording Without Bots for Mac and Windows
Notta’s latest Bot-Free mode is transforming the way professionals capture and transcribe meetings—eliminating interruptions, waiting times, and those uncomfortable moments of “who invited that person?” If you've ever utilized an AI meeting assistant, you're familiar with the scenario. You're engaged in a conversation, the dialogue is starting to pick up speed, and suddenly, a bot enters the call. Everything comes to a halt. […]
 ChatGPT, Gemini, and other AI bots often provide poor medical advice about half the time.
A study published in BMJ Open discovered that five prominent AI chatbots frequently provided inaccurate health recommendations, with open-ended inquiries leading to the poorest responses and the quality of citations deteriorating upon examination.
ChatGPT, Gemini, and other AI bots often provide poor medical advice about half the time.
A study published in BMJ Open discovered that five prominent AI chatbots frequently provided inaccurate health recommendations, with open-ended inquiries leading to the poorest responses and the quality of citations deteriorating upon examination.
More than 30 WordPress plugins purchased on Flippa have been compromised through a backdoor in a supply chain attack.
A hacker acquired over 30 WordPress plugins on Flippa, embedded backdoors that remained inactive for eight months, and then triggered disguised SEO spam visible only to Googlebot. WordPress does not conduct ownership-transfer inspections.
