Mozilla has addressed 271 vulnerabilities in Firefox that were identified by Anthropic's Claude Mythos during a single evaluation process.
Summary: Mozilla has launched Firefox 150, addressing 271 security vulnerabilities uncovered by Anthropic’s Claude Mythos Preview, an unreleased frontier AI model limited to select organizations under the Project Glasswing initiative. The collaboration initiated earlier this year, with Claude Opus 4.6 identifying 22 bugs in Firefox 148; Mythos subsequently detected over twelve times that amount. Bobby Holley, Firefox CTO, noted that these defects are “finite” and emphasized that defenders can now potentially identify all of them. The UK AI Security Institute has confirmed that Mythos is capable of executing autonomous multi-stage network attacks, raising concerns about dual-use capabilities.
Mozilla unveiled Firefox 150 on Monday to patch 271 security vulnerabilities identified by Anthropic’s Claude Mythos Preview, a frontier AI model limited to select organizations as part of Project Glasswing. The significant aspect is not the complexity of the bugs but their accessibility; Mozilla stated they had not encountered any issues that could not have been discovered by a skilled human researcher. In a blog post titled “The zero-days are numbered,” Mozilla highlighted that no human team could have identified 271 vulnerabilities in such a short time.
Mozilla’s partnership with Anthropic commenced earlier this year with a more modest approach. In February, Firefox’s security team utilized Claude Opus 4.6 to analyze nearly 6,000 C++ files within the browser’s codebase. This effort resulted in 112 unique reports, with 22 confirmed as security-related bugs that were fixed in Firefox 148. Of these, fourteen were classified as high severity, constituting nearly a fifth of all high-severity vulnerabilities addressed in Firefox for 2025. The subsequent assessment by Mythos revealed more than twelve times the number of confirmed vulnerabilities. Bobby Holley described this experience as giving the team “vertigo.”
Claude Mythos Preview is the model central to Anthropic’s restricted Mythos model program, Project Glasswing, which was announced on April 7. It is a general-purpose frontier model, not designed solely for security, yet its coding abilities have reached a threshold significant enough for controlled distribution. The UK’s AI Security Institute evaluated the model and determined it could conduct multi-stage network attacks autonomously, completing a 32-step corporate network attack simulation called “The Last Ones” in three out of ten trials. It can combine multiple small vulnerabilities into a potent attack, reconstruct source code from deployed software to identify exploitable weaknesses, and develop custom tools for movement and data extraction within a network.
Access is limited to 12 named launch partners, such as Amazon Web Services, Apple, Broadcom, Cisco, CrowdStrike, Google, JPMorgan Chase, the Linux Foundation, Microsoft, Nvidia, and Palo Alto Networks, with around 40 additional organizations permitted access for defensive security purposes. Anthropic has allocated up to $100 million in usage credits and $4 million in direct contributions to open-source security organizations, including $2.5 million to Alpha-Omega and OpenSSF via the Linux Foundation and $1.5 million to the Apache Software Foundation. The model is accessible to Glasswing participants at a rate of $25 per million input tokens and $125 per million output tokens through platforms such as Claude API, Amazon Bedrock, Google Cloud’s Vertex AI, and Microsoft Foundry.
The restricted rollout has already faced challenges. On the same day Anthropic announced Glasswing, a group of unauthorized users managed to access Mythos Preview by guessing its URL through a third-party vendor environment, an incident that Anthropic is currently investigating.
Holley positioned the 271 vulnerabilities as not a reflection of Firefox’s code quality, but as an indication that the security landscape is shifting in favor of defenders. He noted that a gap between machine-discoverable and human-discoverable bugs had benefitted attackers, who can invest considerable time to uncover a single bug. “Closing this gap erodes the attacker’s long-term advantage by making all discoveries affordable,” he stated.
The rationale is clear. A zero-day vulnerability is particularly valuable to an attacker as long as it remains unknown. If a defender can discover and patch the bug prior to the attacker, the vulnerability loses its offensive potential. Historically, the cost asymmetry has favored attackers: a browser like Firefox comprises millions of lines of code, making even a single undiscovered flaw exploitable. An elite security researcher might invest weeks or months to locate one such flaw, whereas a model like Mythos can examine the entire codebase in a fraction of that time. Mozilla argues that this shifts the economic balance permanently. “Software like Firefox is designed in a modular way for humans to evaluate its correctness,” the blog post explained. “It is complex but not arbitrarily so. The defects are finite, and we are moving towards a scenario where we can finally identify them all.”
This assertion is bold and intentionally so. Mozilla posits that the era of zero-day vulnerabilities in well-structured software has a finite timeline, not because attackers will cease their efforts,
Other articles
 SpaceX S-1 cautions that orbital AI data centers might not be feasible, just months after Musk referred to space-based AI as an obvious choice.
SpaceX's filing prior to its IPO indicates that space data centers rely on untested technology and might not be feasible. Musk mentioned at Davos that they could become the most cost-effective solution within three years.
SpaceX S-1 cautions that orbital AI data centers might not be feasible, just months after Musk referred to space-based AI as an obvious choice.
SpaceX's filing prior to its IPO indicates that space data centers rely on untested technology and might not be feasible. Musk mentioned at Davos that they could become the most cost-effective solution within three years.
 Gemini can now generate documents, slides, meetings, and additional items in chat.
Google has incorporated Gemini into Chat, enabling users to generate documents, slides, and handle tasks directly within their conversations.
Gemini can now generate documents, slides, meetings, and additional items in chat.
Google has incorporated Gemini into Chat, enabling users to generate documents, slides, and handle tasks directly within their conversations.
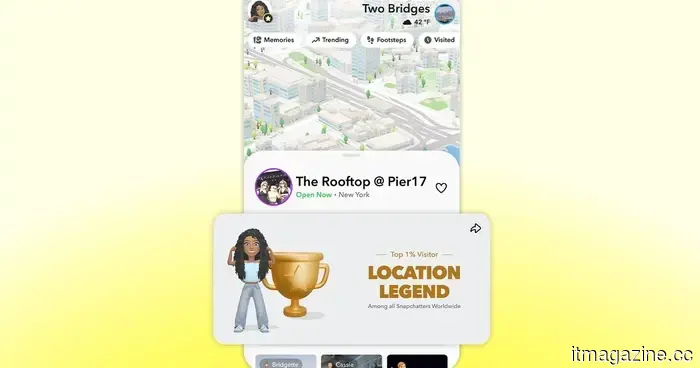 Snapchat Place Loyalty introduces a competitive element to Snap Map.
Snapchat has launched Place Loyalty, a new feature on Snap Map that offers tiered badges for frequent visits, transforming regular hangouts into something to proudly display.
Snapchat Place Loyalty introduces a competitive element to Snap Map.
Snapchat has launched Place Loyalty, a new feature on Snap Map that offers tiered badges for frequent visits, transforming regular hangouts into something to proudly display.
 The facelifted BMW i7 features Gen6 cells sourced from Rimac, offers a range exceeding 350 miles, and replaces Level 3 with a more affordable Symbiotic Drive.
The 2027 BMW i7 is equipped with Rimac-designed Gen6 cylindrical cells, has a capacity of 112.5 kWh, supports 250 kW charging, and offers an EPA range of over 350 miles. Production will commence in July at the Dingolfing facility.
The facelifted BMW i7 features Gen6 cells sourced from Rimac, offers a range exceeding 350 miles, and replaces Level 3 with a more affordable Symbiotic Drive.
The 2027 BMW i7 is equipped with Rimac-designed Gen6 cylindrical cells, has a capacity of 112.5 kWh, supports 250 kW charging, and offers an EPA range of over 350 miles. Production will commence in July at the Dingolfing facility.
 Pichai kicks off Cloud Next 2026 with a $240 billion backlog, 750 million Gemini users, and a strategy to transform Search into an agent manager.
Google Cloud surpassed $70 billion in revenue, showing a 48% growth, with a backlog of $240 billion. Pichai mentioned that Search will evolve into an agent manager. Capital expenditures have doubled to $185 billion.
Pichai kicks off Cloud Next 2026 with a $240 billion backlog, 750 million Gemini users, and a strategy to transform Search into an agent manager.
Google Cloud surpassed $70 billion in revenue, showing a 48% growth, with a backlog of $240 billion. Pichai mentioned that Search will evolve into an agent manager. Capital expenditures have doubled to $185 billion.
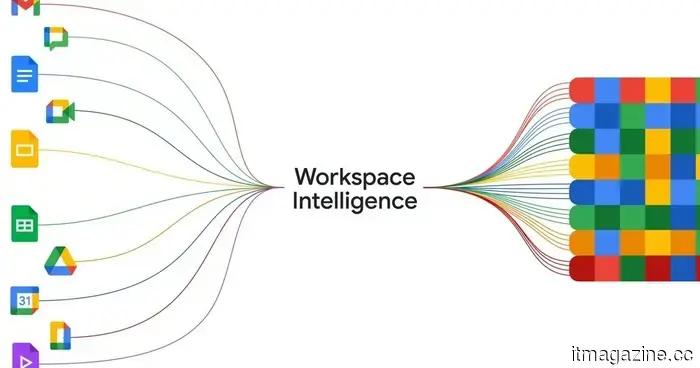
 Workspace Intelligence transforms Gemini into a comprehensive AI agent capable of handling all aspects of your work.
A couple of weeks ago, Google unveiled a new feature named Personal Intelligence. Essentially, it allows Gemini to access the content saved in your Gmail inbox and Photos library. The next time you query the AI about travel plans, projects, or other pertinent matters, it will effortlessly refer to your saved information to provide useful responses, […]
Workspace Intelligence transforms Gemini into a comprehensive AI agent capable of handling all aspects of your work.
A couple of weeks ago, Google unveiled a new feature named Personal Intelligence. Essentially, it allows Gemini to access the content saved in your Gmail inbox and Photos library. The next time you query the AI about travel plans, projects, or other pertinent matters, it will effortlessly refer to your saved information to provide useful responses, […]
Mozilla has addressed 271 vulnerabilities in Firefox that were identified by Anthropic's Claude Mythos during a single evaluation process.
Firefox 150 includes 271 bug fixes identified by Claude Mythos Preview. Mozilla states that the issues are limited. The UK AI Security Institute indicates that the model has the capability to conduct autonomous attacks as well.
