
Hackers compromised Poland's water treatment facilities by exploiting default passwords, while the US encounters similar threats to its critical infrastructure.
Hackers infiltrated five Polish water treatment facilities in 2025 by exploiting default passwords and control systems that were directly accessible on the internet. Poland is investing one billion euros in cybersecurity; meanwhile, 70 percent of American water utilities do not meet basic cybersecurity standards.
In May 2025, an unauthorized individual accessed the supervisory control system in Szczytno, adjusting flushing cycles while the facility was under live monitoring. In Jabłonna Lacka, a video captured an intruder logging in through an admin account to change settings on pumps and filters. The ABW (Poland's Internal Security Agency) indicated that these attackers could manipulate technical settings, creating "a direct risk" to water supply operations.
The agency identified two main vulnerabilities: the use of factory-default passwords and industrial control systems that were publicly exposed online. Exploiting these weaknesses does not require advanced tools and has been documented in cybersecurity advice for more than a decade. The ABW report mentioned Russian APT groups such as APT28 and APT29, along with the Belarusian group UNC1151, targeting Polish entities, although it refrained from directly linking specific breaches to particular groups. Poland's government claims the nation faces between 20 and 50 cyberattacks daily.
After the election of its pro-Ukraine government, cyberattacks on Poland increased significantly, with a coordinated attack in December 2025 targeting a heat and power plant serving nearly 500,000 customers, attributed to the Russian-linked group Sandworm. Poland's cybersecurity budget for 2026 has reached a record one billion euros, rising from 600 million in 2024. Specifically, 80 million euros is set aside for enhancing cyber defenses in water management. Although Germany dominates Europe's defense tech funding, Poland's per-capita cybersecurity spending now surpasses that of most NATO countries.
This financial commitment indicates an acknowledgment that threats have evolved beyond mere espionage. The European military AI startup Helsing raised 450 million euros to bolster NATO defenses against Russia, while Ukraine's growing defense tech capabilities highlight the need for countries bordering Russia to enhance their defense readiness. However, the breaches at the water treatment facilities in Jabłonna Lacka and Szczytno were due to basic oversights rather than sophisticated hacking methods.
In the United States, a similar vulnerability exists on a larger scale. In 2024, the Environmental Protection Agency revealed that nearly 70 percent of inspected water utilities did not comply with basic cybersecurity standards, including failing to change default passwords. American Water, the country's largest regulated water and wastewater utility, had to shut down its billing systems in October 2024 due to a cyberattack.
The dangers are real. The Chinese state-sponsored group Volt Typhoon has breached the IT systems of various U.S. critical infrastructure organizations, including water systems. The Iranian-affiliated group CyberAv3ngers has also targeted programmable logic controllers at U.S. water facilities. Despite multiple advisories from the EPA, CISA, and the FBI, the small municipal systems lacking resources, capable infrastructure, and dedicated cybersecurity staff are the least likely to adopt necessary precautions.
While European defense stocks surge due to government investment in military technology and Poland allocates substantial funds for cybersecurity, the water treatment plants that were compromised were unprotected. Facilities in Jabłonna Lacka and Szczytno operated with factory-default credentials that were exposed online. The U.S. utilities identified as violators by the EPA faced the same situation. The level of sophistication of an attacker matters little when easy access is available.
The ABW's recent activity summary underscores the urgency of the situation, as the scale of the threat has rendered silence impossible. Although the U.S. has issued numerous advisories, there remains a consistent pattern: the governments that best understand the cybersecurity risks confronting them are often those whose critical infrastructures remain most vulnerable. Water treatment systems are generally managed by municipalities with inadequate resources, expertise, or regulatory pressures to secure them. The hackers who targeted the five Polish facilities did not require advanced exploits; they simply needed a password.
Other articles
 The Top Thunderbolt 5 Docks for Mac in 2026
Don't continue to accept docks that restrict your Mac's ability to deliver a smooth desktop-grade experience daily. As we conclude the top Thunderbolt 5 docks for Mac in 2026, explore the premier docking stations that transform cable clutter into an efficient multi-display arrangement.
The Top Thunderbolt 5 Docks for Mac in 2026
Don't continue to accept docks that restrict your Mac's ability to deliver a smooth desktop-grade experience daily. As we conclude the top Thunderbolt 5 docks for Mac in 2026, explore the premier docking stations that transform cable clutter into an efficient multi-display arrangement.
 Netflix is trialing its own voice search functionality, which appears to be less frustrating.
Netflix is experimenting with a built-in AI-driven voice search feature that enables users to discover shows based on mood or vibe, providing text-based results without any personalization for the time being.
Netflix is trialing its own voice search functionality, which appears to be less frustrating.
Netflix is experimenting with a built-in AI-driven voice search feature that enables users to discover shows based on mood or vibe, providing text-based results without any personalization for the time being.
 Netflix is experimenting with its own voice search functionality, which appears to be less aggravating.
Netflix is experimenting with a built-in AI-driven voice search feature that allows users to discover shows based on mood or vibe, currently providing text-based results without any personalization.
Netflix is experimenting with its own voice search functionality, which appears to be less aggravating.
Netflix is experimenting with a built-in AI-driven voice search feature that allows users to discover shows based on mood or vibe, currently providing text-based results without any personalization.
 Meta aims to develop an AI agent that will shop on Instagram on your behalf, performing the role of an agent.
Meta is said to be developing AI tools designed to handle daily tasks, including an Instagram shopping assistant anticipated for late 2026.
Meta aims to develop an AI agent that will shop on Instagram on your behalf, performing the role of an agent.
Meta is said to be developing AI tools designed to handle daily tasks, including an Instagram shopping assistant anticipated for late 2026.
 Whoop's reply to Fitbit Air and Google Health involves actual doctors rather than just an AI chatbot.
Google relies on Gemini to support your health, while Whoop is introducing a licensed physician to your display. Here’s what each method truly signifies for your financial situation and your health.
Whoop's reply to Fitbit Air and Google Health involves actual doctors rather than just an AI chatbot.
Google relies on Gemini to support your health, while Whoop is introducing a licensed physician to your display. Here’s what each method truly signifies for your financial situation and your health.
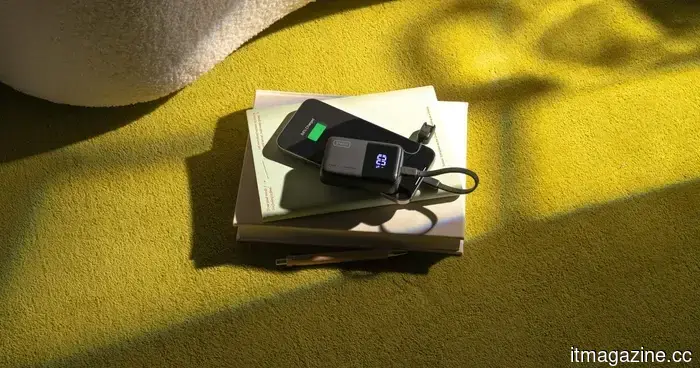 The INIU Pocket Rocket P50 is the tiniest power bank that your pocket truly requires.
Fed up with lugging around heavy power banks wherever you venture? The INIU Pocket Rocket P50 combines 10,000mAh capacity with 45W fast charging in a compact, macaron-sized form that easily fits in your pocket, ensuring you stay powered throughout the day, free from tangled cords or the hassle of searching for outlets.
The INIU Pocket Rocket P50 is the tiniest power bank that your pocket truly requires.
Fed up with lugging around heavy power banks wherever you venture? The INIU Pocket Rocket P50 combines 10,000mAh capacity with 45W fast charging in a compact, macaron-sized form that easily fits in your pocket, ensuring you stay powered throughout the day, free from tangled cords or the hassle of searching for outlets.
Hackers compromised Poland's water treatment facilities by exploiting default passwords, while the US encounters similar threats to its critical infrastructure.
Poland's ABW revealed that five water treatment facilities experienced ICS breaches due to the use of default passwords. The US EPA identified that 70% of American water utilities do not meet fundamental cybersecurity standards.
