
A future without passwords is still several years off.
Since around 2018, the cybersecurity sector has been proclaiming the demise of passwords, touting replacements like passkeys, biometrics, and FIDO2 hardware tokens. The allure of this transition is compelling: eliminating breached vaults, credential stuffing, and sticky notes on screens.
However, this shift has not materialized on a large scale. According to a March 2026 report from HYPR, an identity security firm, 76 percent of organizations still depend on traditional passwords as their main method of authentication. Merely 43 percent have implemented any sort of passwordless authentication, and among those, the majority have applied it to fewer than half of their employees. Additionally, the 2025 Verizon Data Breach Investigations Report revealed that stolen credentials were the entry point in 22 percent of all analyzed breaches, with an alarming 88 percent of web application breaches involving compromised passwords.
A passwordless future is indeed on the horizon, yet it remains years away for most companies. The overlooked question is: what should businesses do in the interim?
**The Transition Gap**
The cybersecurity industry suffers from a terminology issue. "Passwordless" conveys a simplistic binary choice: either passwords are used, or they are not. In reality, organizations find themselves on a continuum. A company might utilize passkeys for its primary Single Sign-On (SSO) portal but still depend on conventional credentials for legacy applications, third-party tools, shared infrastructure accounts, and client-facing systems that lack modern authentication protocols.
This scenario creates what HYPR refers to as the “Age of Industrialisation” for identity security: the challenging but necessary task of operationalizing passwordless solutions across disjointed IT environments while securing existing credential-based systems.
Small and medium-sized businesses (SMBs) face this challenge even more acutely. Large firms can allocate teams to multi-year identity transformation initiatives, hiring identity architects, executing 18-month migration plans, and negotiating enterprise licenses with providers like Okta or CyberArk. In contrast, a 30-person marketing agency or a 200-person logistics firm cannot afford the same resources. They require effective password management immediately, along with a feasible strategy for strengthening authentication as it becomes viable.
The transition gap is not a fleeting issue. Research from Gartner indicates that even organizations actively investing in passwordless systems are unlikely to fully phase out traditional passwords before 2028. Legacy applications, regulatory mandates for specific authentication methods, and the inherent complexity of migrating thousands of stored credentials mean that passwords will persist alongside newer authentication technologies for years to come.
This coexistence is often where the majority of breaches occur. Not in the shiny new SSO portal, but in ignored shared spreadsheets of API keys, outdated CRMs still accepting "password123," and contractor accounts that were never deactivated after project completion.
**The Credential Crisis in Numbers**
The urgency of the situation is not just theoretical. The 2025 Verizon Data Breach Investigations Report found that credential stuffing constituted a median of 19 percent of all authentication attempts against SSO providers. Merely three percent of compromised passwords met basic complexity standards. In typical cases, users shared 51 percent of their passwords across various services, causing a single breach to amplify into multiple incidents.
For SMBs, the repercussions are especially severe. Research by NinjaOne and VikingCloud suggests that the average breach costs a business with less than 500 employees $3.31 million, while downtime alone averages about $53,000 per hour. By 2026, an estimated 46 percent of successful cyberattacks on SMBs will stem from credential reuse, increasing from 33 percent in 2023.
The pattern is unmistakable: companies that perceive password management as a resolved issue or as something soon to be outdated are the most vulnerable.
This reflects a cognitive bias at play. The allure of passwordless authentication allows organizations to justify underinvesting in password security presently. The reasoning behind "Why invest in a password manager if passwords are soon to be obsolete?" may seem logical until one acknowledges that 76 percent of businesses still rely on passwords and will continue to do so for years ahead. It's comparable to a homeowner ignoring a leaking roof because they plan to renovate later; the leak won’t wait.
**What "Good Enough" Password Management Looks Like in 2026**
The password management market has seen considerable growth. Mordor Intelligence forecasts it will reach $8.07 billion by 2031, expanding at an annual rate of 22.39 percent. Nonetheless, the market is also bifurcating. On one side, consumer-oriented tools differentiate themselves with features like polish, browser autofill, and app integrations. On the other, enterprise identity platforms (e.g., Okta, Microsoft Entra, CyberArk) incorporate password vaults into comprehensive access governance suites costing tens of thousands of dollars each year.
In between lies a growing array of business-grade password managers aimed at providing enterprise security features at prices accessible to SMBs. The most crucial
Other articles
 File sharing on the Galaxy S26 has become easier with the addition of AirDrop support.
Samsung will launch a global rollout of AirDrop-like sharing for the Galaxy S26, starting on March 23, through its Quick Share feature.
File sharing on the Galaxy S26 has become easier with the addition of AirDrop support.
Samsung will launch a global rollout of AirDrop-like sharing for the Galaxy S26, starting on March 23, through its Quick Share feature.
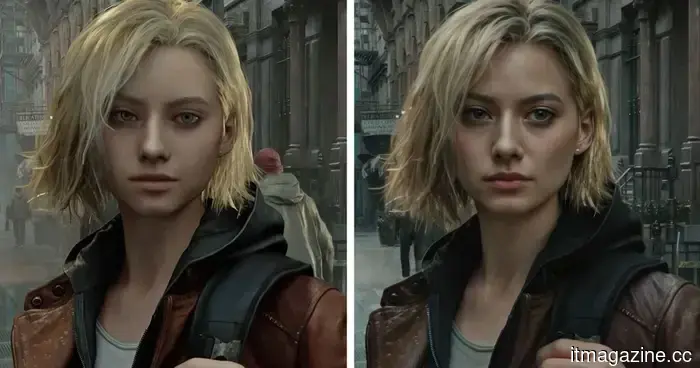 Nvidia DLSS 5 could represent the future of graphics, but I still wish for a large "Off" switch.
DLSS 5 could represent the most significant advancement in real-time graphics for years, yet its AI-filter appearance, computational expenses, and associated risks cannot be overlooked.
Nvidia DLSS 5 could represent the future of graphics, but I still wish for a large "Off" switch.
DLSS 5 could represent the most significant advancement in real-time graphics for years, yet its AI-filter appearance, computational expenses, and associated risks cannot be overlooked.
 OpenAI is in discussions to purchase fusion energy from Helion.
OpenAI is currently in discussions to acquire fusion energy from Helion. Sam Altman has resigned from Helion’s board prior to the negotiations.
OpenAI is in discussions to purchase fusion energy from Helion.
OpenAI is currently in discussions to acquire fusion energy from Helion. Sam Altman has resigned from Helion’s board prior to the negotiations.
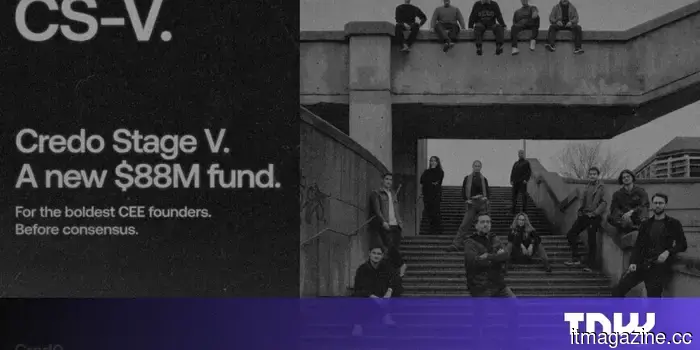 Credo Ventures finalizes its fifth fund at $88 million to continue being the initial investor for the most ambitious founders in Central and Eastern Europe.
The firm based in Prague and Krakow, known for its initial investments in UiPath and ElevenLabs, is intensifying its focus on pre-seed funding in Central and Eastern Europe as well as among its global diaspora. They have a team of six partners and typically write checks ranging from $1 million to $5 million. Credo Ventures has finalized its funding.
Credo Ventures finalizes its fifth fund at $88 million to continue being the initial investor for the most ambitious founders in Central and Eastern Europe.
The firm based in Prague and Krakow, known for its initial investments in UiPath and ElevenLabs, is intensifying its focus on pre-seed funding in Central and Eastern Europe as well as among its global diaspora. They have a team of six partners and typically write checks ranging from $1 million to $5 million. Credo Ventures has finalized its funding.
 The Munich-based startup Interloom secured $16.5 million in funding.
Munich-based startup Interloom has secured $16.5 million in funding, led by DN Capital, to develop a system that continuously updates how businesses make operational decisions.
The Munich-based startup Interloom secured $16.5 million in funding.
Munich-based startup Interloom has secured $16.5 million in funding, led by DN Capital, to develop a system that continuously updates how businesses make operational decisions.
 Nvidia DLSS 5 could represent the future of graphics, but I still wish for a large "Off" switch.
DLSS 5 could represent the most significant advancement in real-time graphics in years, yet its AI-filtered appearance, computational expense, and associated risks cannot be overlooked.
Nvidia DLSS 5 could represent the future of graphics, but I still wish for a large "Off" switch.
DLSS 5 could represent the most significant advancement in real-time graphics in years, yet its AI-filtered appearance, computational expense, and associated risks cannot be overlooked.
A future without passwords is still several years off.
Despite the push for passwordless solutions, 76% of organizations continue to depend on passwords. The true cybersecurity challenge in 2026 will be to manage credentials securely.
